Stellar Edge 3103804503 Cyber Flow

Stellar Edge 3103804503 Cyber Flow presents a modular framework for monitoring, routing, and optimizing network movement across diverse environments. It emphasizes real-time adaptation, auditable decisions, and clear governance boundaries. The system produces a unified data representation to apply policies consistently, mapping varied formats and topologies into common routing logic. Edge-first security scales with enforcement and continuous monitoring, yet relies on balanced metrics and transparent accountability. The implications for autonomy and resilience invite further examination.
What Is Stellar Edge 3103804503 Cyber Flow?
What is Stellar Edge 3103804503 Cyber Flow? The term denotes a defined framework within which Stellar Edge and Cyber Flow operate to monitor, route, and optimize network movements. It emphasizes modular components, interoperability, and real-time adaptation. The description remains neutral, focused, and measurable, ensuring stakeholders understand capabilities, boundaries, and governance without superfluous detail.
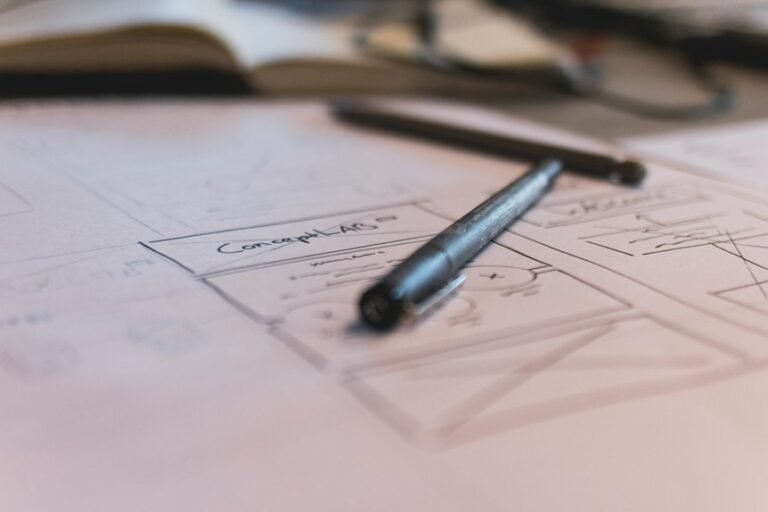
How Cyber Flow Maps Data Across Heterogeneous Networks?
Cyber Flow maps data across heterogeneous networks by translating diverse data formats, protocols, and topologies into a unified representation that supports consistent policy application and routing decisions. It emphasizes data governance and clarifies network topology relationships, enabling interoperable flows and auditable decisions.
The approach remains disciplined, scalable, and architecture-aware, ensuring governance-informed, topology-conscious routing without prescriptive constraints on autonomy or freedom.
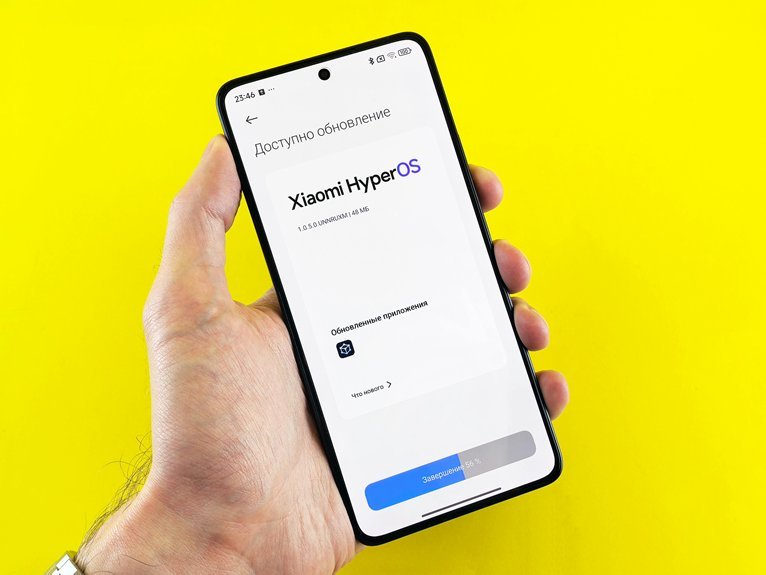
Use Cases: Edge-First Security at Scale
Edge-first security at scale targets distributed surfaces by enforcing policy and protection at the network edge, where traffic originates or terminates.
The use cases emphasize scalable enforcement, continuous monitoring, and rapid containment across diverse environments.
edge security enables proactive posture management and automated responses, while data mapping clarifies trust boundaries, assists policy translation, and informs incident containment without impeding performance.
Evaluating Risk, Pitfalls, and Success Metrics
Pitfalls include overconfidence and misaligned incentives.
Effective metrics balance governance and performance, clarify ownership, and track data governance compliance, ensuring transparent accountability while preserving autonomy and freedom for stakeholders within a resilient cyber workflow.
Conclusion
In the quiet hum of interconnected systems, Cyber Flow threads diverse formats into a single, luminous braid. Data moves like a predictable current across borderless channels, guided by clear governance and auditable choices. Real-time adaptation acts as a compass, steering edge devices toward resilience. Across heterogeneous networks, the framework’s edge-first posture shines: scalable enforcement, continuous monitoring, and proactive risk management harmonize into a dependable, transparent orchestration of cyber movement. A poised, resilient data ecosystem emerges.