Spam Alert and Review of 8778558844 and User Feedback

The piece examines spam risk and user feedback surrounding 877-855-8844, noting consistent caller IDs and neutral scripts alongside occasional urgency tactics. It contrasts reliable, evidence-based warnings with noise, highlighting the importance of verifiable caller verification and practical protections. The discussion points to clear criteria, transparency, and informed consent in safety decisions. As conclusions form, readers are prompted to consider how to apply these insights to real-world protections and next steps.
What 877-855-8844 Looks Like to Callers
Callers often encounter a mix of distinctive cues when interacting with 877-855-8844, shaping their initial perception of the number. The presentation includes a concise caller ID, standard greeting prompts, and neutral scripting. Visual and auditory cues emphasize reliability. Two word discussion ideas, spam alerts, and clear identification support informed judgments while maintaining a calm, freedom-minded, factual tone for readers.
Red Flags and Common Tactics Reported
The reporting emphasizes abrupt deadlines, vague caller identities, and insistence on immediate action. Observers classify these as manipulative red flags and common tactics designed to provoke anxiety, bypass skepticism, and extract data, undermining user autonomy and privacy.
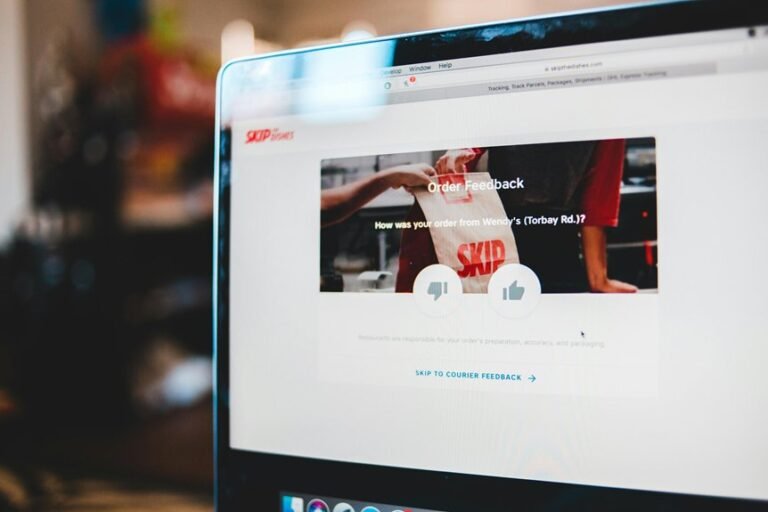
Evaluating Warnings: Trustworthy Reviews vs. Noise
Evaluating warnings about 877-855-8844 requires distinguishing between trustworthy reviews and noise driven by sensationalism or bias. This assessment identifies fraud indicators without sensationalism, emphasizing evidence over rhetoric.
Listener analysis notes caller skepticism as a healthy stance, prompting corroboration across sources.
Clear criteria help separate credible experiences from misreporting; precision supports informed decisions and freedom from undue pressure.
Practical, Real- World Protections and Next Steps
The discussion emphasizes verified scam detection methods, caller verification, and user empowerment without sacrificing autonomy.
Safety implications include informed consent and privacy considerations.
Implemented protections should be transparent, interoperable, and adaptable, enabling individuals to assess risk while maintaining freedom from coercive practices.
Conclusion
The thread of caution winds around the phone like a quiet clock, where a precise dial tone marks the beat of scrutiny. Shadows of urgency and anonymous numbers mingle with verifiable cues and measured claims, each step a lantern in the fog. Trust grows when verifiable verification meets practical safeguards, not pressure. In this landscape, clarity is the compass, and informed consent the shore, guiding users to navigate noise toward transparent, evidence-based protection. Silence the sensational, illuminate with facts.